Writing a good cover letter must pay attention to several important aspects, including diction, proper vocabulary, to grammar. Besides, you also need to pay attention to the content of the application you make so you can convince the recruiter, especially if you want to apply for an important position. You have to understand what aspects are required, what language is good, and what is the most professional format. In this article, we will invite you to discuss tips on writing the right interpersonal communication cover letter.
Contents
What Are The Important Interpersonal Skills?
One of the most important skills that recruiters will consider you are your good interpersonal skills. The following is a list of interpersonal skills that you must have if you want to pursue interpersonal communication:
- Have excellent communication skills in any method
- Good at negotiating with other people
- Able to be a good listener
- Can make a decision well and professionally
- Able to solve various problems faced
- Decisive, patient, and full of empathy
- 4+ Excel Project Management Template
- 4+ event planning template sample
- 5+ rental application template sample
- Printable Family Tree Form
- 3+ Basic Html Template
How To Write A Good Cover Letter For Interpersonal Skills?
To write a good and professional interpersonal communication cover letter, you need to include several important aspects of your resume. Include stories in the form of facts or examples about the development of your interpersonal skills, so that recruiters can believe that you are talented.
You will need to relate the experience you have to the job you are currently applying for. Remember some of the things in the past that will bring a big impact and showed that you have amazing interpersonal skills.
How To Improve Interpersonal Skills?
To improve interpersonal skills, you can apply the following tips:
- Make elegant gestures so others don’t think you are too aggressive or rushed
- Start practicing listening to all the family members or friends who are talking, listen carefully and accurately
- Often practice presentation or lead
- Communicate with others politely and enthusiastically
- Do everything with confidence
Interpersonal Communication Cover Letter Sample
If you are unsure to start writing your cover letter, you can see one of the examples we have prepared below:
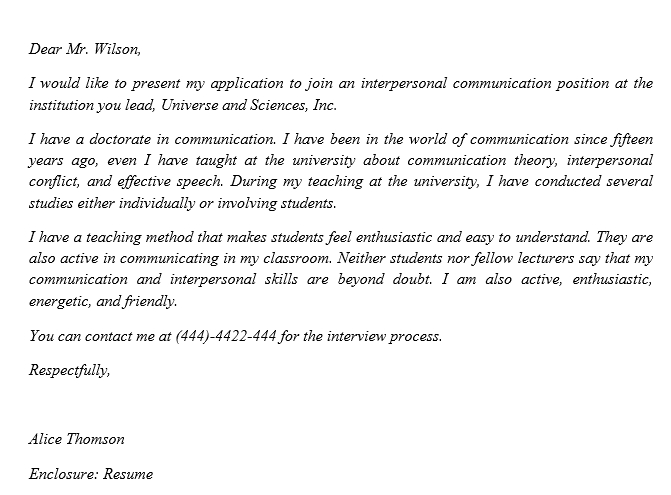
Dear Mr. Wilson,
I would like to present my application to join an interpersonal communication position at the institution you lead, Universe and Sciences, Inc.
I have a doctorate in communication. I have been in the world of communication since fifteen years ago, even I have taught at the university about communication theory, interpersonal conflict, and effective speech. During my teaching at the university, I have conducted several studies either individually or involving students.
I have a teaching method that makes students feel enthusiastic and easy to understand. They are also active in communicating in my classroom. Neither students nor fellow lecturers say that my communication and interpersonal skills are beyond doubt. I am also active, enthusiastic, energetic, and friendly.
You can contact me at (444)-4422-444 for the interview process.
Respectfully,
Alice Thomson
Enclosure: Resume
That’s all our brief explanation about an interpersonal communication cover letter and its sample. Hope it can help you a lot in writing your format.